AT&T Employees Use Decoy Number to Steal Customer SIM Card
There’s a part at the bottom that I promise will blow your freaking mind!
TOPIC / Identity TheftI’m not sure why the employee agreed to my recording it, but this incident unfolded over two and a half hours. It’s been nearly a month since I first reported this to the authorities, and the lack of a response suggests it is far more common than I realized.
AT&T had relatively strong security measures that initially blocked employees from pulling this off, but they were persistent; it took them nearly two hours. Without AT&T’s “Extra Security” feature, it would have taken 10-15 minutes.
AT&T’s identity verification system couldn’t prevent the employees from stealing my SIM card and account information, but it did generate enough information to prove what happened. I’ll share which verification systems are available and how to activate them to protect your account.
This was my third attempt in nearly three months to get my SIM card replaced, and I asked to record it because the account information the employees shared, along with their explanation of the process, didn’t make much sense.
Your IMEI is a highly sensitive piece of information.
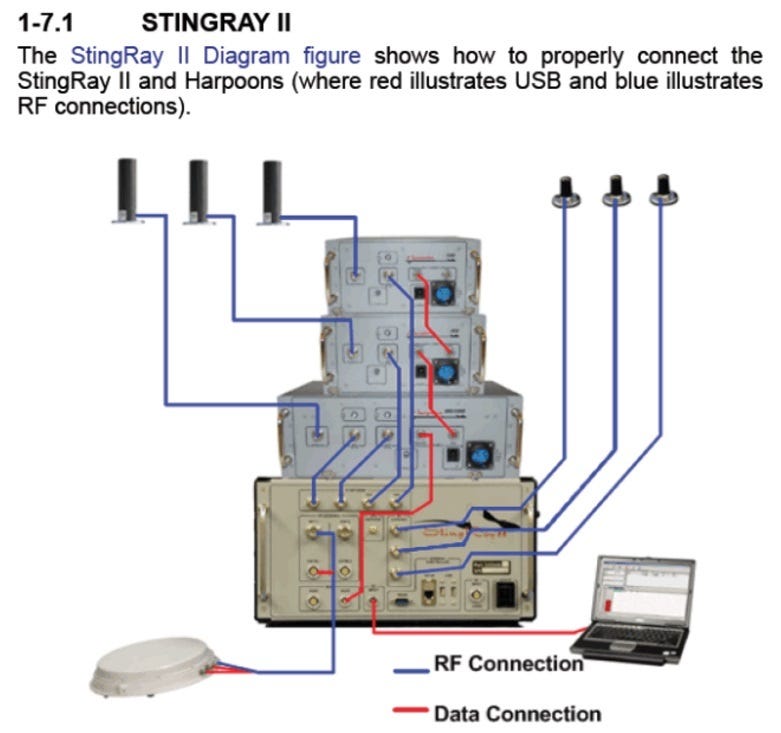
If you pay close attention, you’ll notice that the employees demanded several actions, claiming they were “procedure.” The reason is because of how StingRay wiretap devices work. Because I insisted on a nano-SIM instead of an eSIM, they had to keep me on-site for two hours to activate the SIM card and access my accounts.
In a separate post, I’ll share a video recording of a bank call that was intercepted, in which an impersonator tried to trick me into disclosing my account information.
This Was a Long Con – Here’s the Short Story
This starts with me visiting an AT&T corporate store in West Hollywood, California, to replace a stolen phone and SIM card. Whoever stole my phone removed the SIM card and registered it with their own phone and IMEI, allowing them to intercept my calls and text messages. Specifically, the phone thief used my SIM card to bypass 2FA (two-factor authentication) on my bank and other online accounts.
The employees not only initially lied that they couldn’t see the full IMEI of the phone thief, but also, at one point, walked away with my SIM card and driver’s license and used them to access my account information illegally.
I spent over two hours at the store, simply trying to get a SIM card so I could use my phone. Continue reading below to see how they pulled that off. It’s wild!
You can listen to the full experience at the bottom.
Continue down, and I’ll share the more pertinent moments.
Don’t Be a Victim
Here are some details you should be aware of to prevent falling victim to this sort of scheme: (1) you don’t need an IMEI or eSIM to reactivate your AT&T line, (2) when a phone is lost or stolen, there’s a standard “Stolen Equipment “ status change that employees are supposed to complete.
1. You don’t need a phone, eSIM, or IMEI to get a new SIM or reactivate your line.
Initially, the employee insisted I needed a phone to reactivate my account, saying it’s “procedure.” If that were true, it would mean that once a phone or SIM card is lost, you can’t get a SIM card for a borrowed phone or for a phone purchased later.
Just so you know, it is against policy…
The employee’s claim is incorrect because the SIM card serial number is equivalent to a phone’s IMEI.
For roughly 30 minutes, the employees insisted that I provide an IMEI to activate the line.
I can’t process a SIM without an IMEI.
StingRay devices work by forcing nearby cellphones to connect to a fake cellphone tower. After connecting with the fake tower, the phone will transmit sensitive information such as IMEI, GPS location, and encryption keys. With that information, a fake tower operator can not only track your location but also view your text messages, listen in on your calls, monitor your internet traffic, or initiate fake phone calls that appear (as far as your phone can tell) to come from a legitimate source.
If the fake tower operators don’t know your IMEI number, they have to cycle through all the phones in the area until they land on the right one. That can be done by simply waiting until someone visits their Gmail account, and, based on the username they type on the login page, they can be certain it’s the right person. Or they can just ask you what it is.
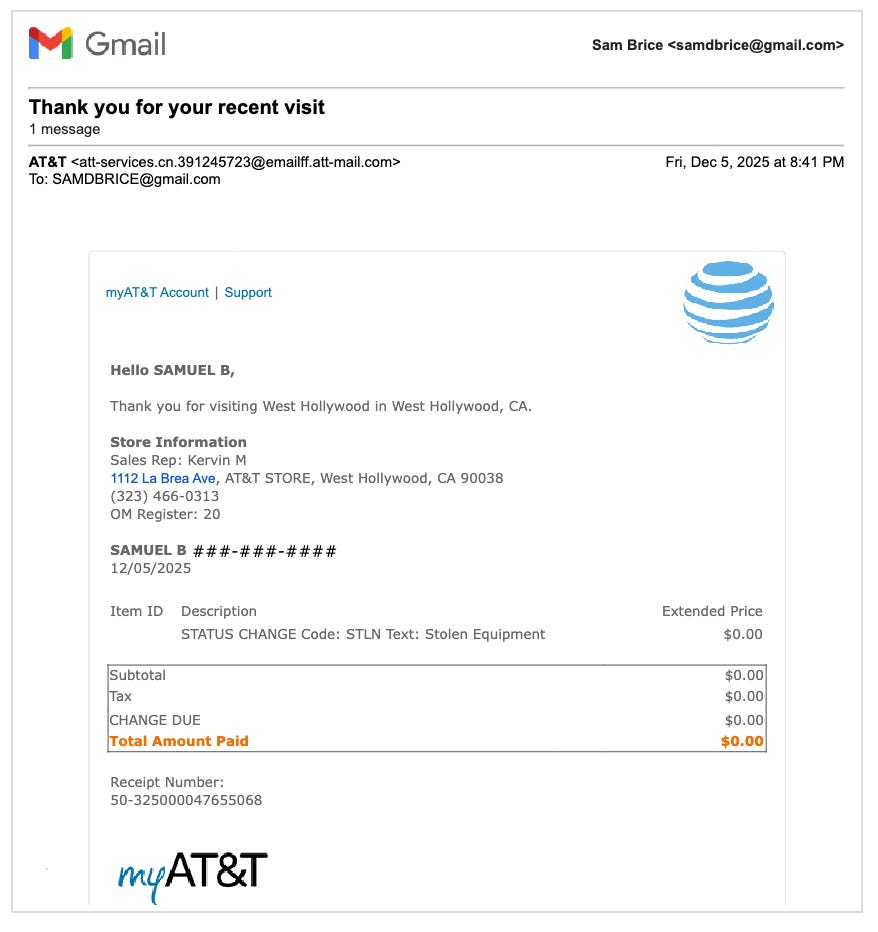
2. There’s a standard “Stolen Equipment” status change employees are supposed to complete once you’ve proven you’re the account owner.
I didn’t really buy the “We require an IMEI” story, so I asked to speak with AT&T Customer Service to detach the stolen phone from my account.
While waiting on a 40-minute hold to speak with Customer Service, one of the employees secretly disconnected the stolen phone from my account, using the proper “Stolen Equipment” status change, as soon as Customer Service came on the line. I received an email notification that not only told me which employee completed the “Stolen Equipment” status change, but also the kiosk that was used.
And of course, I asked the store employees what had just happened, and they said they hadn’t done anything at all!
I didn’t do anything. We haven’t done anything at all.
This is the part that’s going to blow your mind❗️
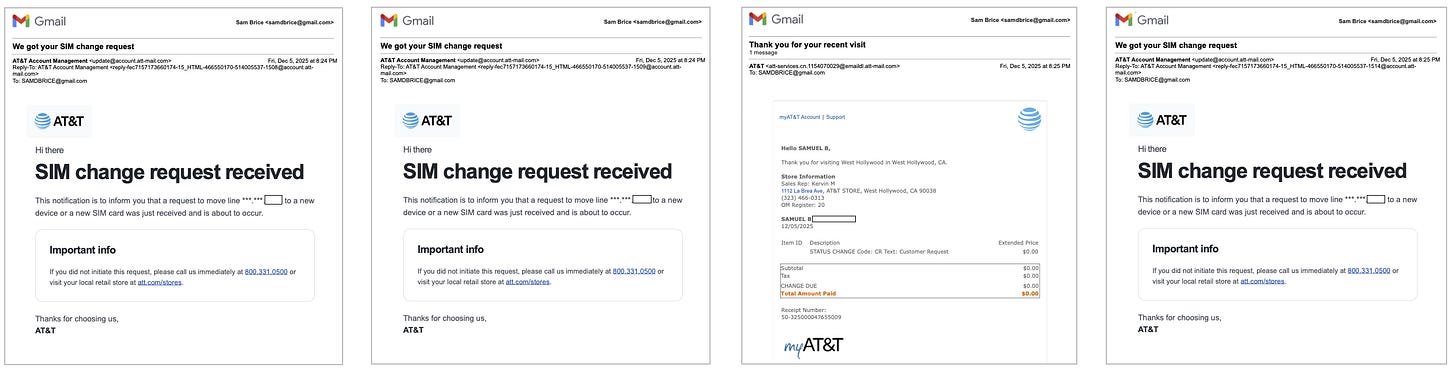
During the 40-minute hold with Customer Service, I received multiple notifications that employees had apparently transferred my line and numbers to different devices.
Which means that during those 40 minutes to an hour, my line had been activated, anything could have happened, with someone placing calls or sending text messages impersonating me to access any of my bank or other accounts registered for 2FA using those numbers.
Throughout that time, the employees claimed nothing was happening.
I haven’t activated anything.
Listen to this.
For ID Verification, AT&T has a special Triage Department that only employees can call.
The Customer Service number I was given was a decoy❗️
We’re gonna have to call into a different [Triage] department…
At one point, the employees took my newly activated SIM cards and my ID to the back of the store. While I was on the line with Customer Service, they were evidently talking to the real Triage Department number to impersonate me.
That’s just wild!
All that time, I’m asking what’s going on, and the response is consistently…
We’ve done nothing…we’re literally at ground zero.
Then LeBron J.R. showed up.
I had some scrap paper I needed to throw away…
That was a really bad Kobe impression. That was LeBron J.R.
Finally, two hours later!
Finally, two hours after I first walked into the store, the employees decided to have mercy on me and call the real Triage Department…
Hello, this is AT&T Triage, my name is Diego…
Then the employee admits that the Customer Service number was never the right number.
That department [Triage] is only for representatives…I called, you can’t call.
Once the real Triage Department was on the line, the SIM transfer took 10 minutes.
The end.
Here’s Kobe!
Thanks for reading, watching, and listening.
If you take away anything from the above, make sure “Extra Security” is enabled on your account. Also, whenever an employee asks for your account PIN, it's best if they hand you the iPad so you can enter it yourself.
When I first walked into the store, I changed my account PIN and didn’t show it to the employees. At the two-hour mark, I finally eased up and just told them the number. There’s a chance that’s the only reason they let me go.
The very next morning, while I was asleep, someone seemingly used my PIN to access and modify my account.
That’s not all.
If you think that was crazy, wait until I show you what happened a few days later.
I’m going to show you what it looks like when a cellphone gets DoS-ed (Denial of Service) by a StingRay.
When your phone gets DoS-ed, your phone line is remotely cut off, and you can’t make or receive calls, texts, or use data. Or even call 911.
Thanks for reading!
If you haven’t signed up yet, do that now.
❤️
Full Recording
PS: This was the third time in three months that something like this happened to me at an AT&T store. I had a really hard time believing what was happening, so to analyse this instance and make sure I wasn’t making stuff up, I created a spreadsheet to cross-reference what the employees were telling me versus what AT&T’s system was saying.
You can check out the sheet here: https://docs.google.com/spreadsheets/d/1MzRqsuM7qvyvBp...68505